 The Internet is a fascinating and wonderful place full of great, informative resources and websites, but it’s also home to online markets for illegal and unethical practices. These hotbeds of criminal activity are a danger not only to your business, but to everyone who uses the Internet.
The Internet is a fascinating and wonderful place full of great, informative resources and websites, but it’s also home to online markets for illegal and unethical practices. These hotbeds of criminal activity are a danger not only to your business, but to everyone who uses the Internet.
Specifically, the Internet (or what’s known as the “dark web”) is often used to anonymously distribute drugs, data, and other questionable activity. The Internet itself allows for anyone to take on a pseudo-anonymous nature, but there are other, much darker parts of the Internet that can only be accessed if you’re truly anonymous. Users who are using the anonymity browser Tor can go about their business on the dark web with little to fear. Many online black markets will only allow users to access them if they’re using Tor, primarily because they want to dodge law enforcement as much as possible.
Not all online black markets take this same precaution, though. Some illegal online markets don’t care about staying available to their buyers or hidden from the authorities, and will even sell to the common masses rather than hardened criminals. This sporadic and unpredictable behavior is one reason why everyone should be concerned about the dark web. Since these underground black markets are often available via the “surface web” (the part that the average user sees), this increases the range and scope of who criminals can target with their goods, which allows the cybercrime industry to thrive.
From Trend Micro via TechRepublic, here’s a chart detailing what the online crime market is primarily used for.
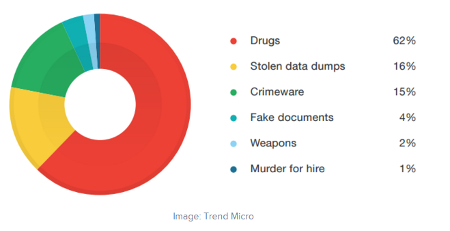
Drugs are one of the biggest components of the online cybercrime industry, but stolen data dumps and crimeware are the second and third largest threats, respectively. A surprising factor, however, is the presence of illegal online arms manufacturing, and even assassinations. When you consider the fact that anyone can access these assets through the surface web, it’s a frightening concept indeed.
The North American underground dark web network is generally considered what’s called a “glass tank.” It might be useful for its intended purpose, but it’s so transparent and fragile that it can shatter and break at any given moment. Trend Micro reports that the life cycle of most black market sites is very short. The sites could be available one moment, and gone the next.
If you take away anything from this blog article, it’s that cybercriminals are as resourceful as they are slippery, and that they’ll use any means necessary to make a quick buck. This includes selling information they’ve stolen from businesses just like yours on the black market, or selling malicious code to would-be hackers. Business owners need to be exceptionally cautious when dealing with criminals on the Internet, simply due to the fact that they’ll attack for no other purpose other than to cause a little bit of chaos and to throw your sensitive data in the “for sale” window. It’s important to remember that there is, in fact, a market for your stolen data, and that hackers will do whatever it takes to breach your systems and make money off of your misfortune.
Total Tech Care knows how to handle the security threats that your business faces every day, and we can outfit your network with the solutions required to eliminate and detect issues before they become bigger problems. Furthermore, we can protect your organization’s end-users from accessing infected or suspicious sites, like potentially malicious web pages, or those designed to sell questionable goods. Perhaps the best way we can protect your business is by offering enterprise-level security solutions, like firewalls, antivirus, content filtering, and spam blocking solutions, effectively mitigating the odds of your business falling prey to a hacking attack.
For more information, give us a call at 866-348-2602.




