 You might be aware that some websites collect personal data from you depending on your mobile device’s location, your browsing history, and several other factors. This information is generally used for marketing, but it could have unforeseen effects on the way you browse the Internet. It can be fairly revealing about your personality, or possibly even incriminating. Therefore, you should be aware of how this personal information is gathered from you without you even knowing it.
You might be aware that some websites collect personal data from you depending on your mobile device’s location, your browsing history, and several other factors. This information is generally used for marketing, but it could have unforeseen effects on the way you browse the Internet. It can be fairly revealing about your personality, or possibly even incriminating. Therefore, you should be aware of how this personal information is gathered from you without you even knowing it.
Here are a few things Forbes magazine suggests you might not know about the gathering of your personal data:
 Marketers Are the New Mom & Pop Store Owners
Marketers Are the New Mom & Pop Store Owners
Remember that man who worked at the old general wares store down the road from you several years ago? He would remember everything about you; your name, your face, your interests, favorite beer, etc. The truth is that he knew most of what you preferred because you visited often and he picked up on patterns in your behavior.
In 1967, Lester Wunderman, the “father of direct marketing,” was able to predict that technology could accomplish this same feat with exponentially larger numbers: “A computer can know and remember as much marketing detail about 200,000,000 customers as did the owner of a crossroads general store about his handful of customers.”
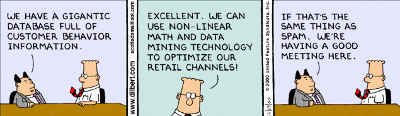
As such, marketers are able to analyze data that computers gather about you and create marketing lists, which includes all types of personal information: religion, political view, marital status, sexual orientation, and more.
Your ZIP Code is Worth a Lot
To a marketer, your ZIP code is an absolute gold mine. You might think nothing of it when you enter your ZIP code at the local grocery store, but you’re giving marketing institutions all of the information they need to find you at a later location for future marketing campaigns. According to a Harvard professor Latanya Sweeney, a company can identify you an alarmingly high 87 percent of the time with only a few of your credentials:
- ZIP code
- Date of birth
- Gender
Even the folks you trust the most with your ZIP code, your local post office, can take advantage of this and sell your information to marketers. The United States Postal Service is continuously validating old addresses and informing marketers when their targets have moved on to another location. According to Forbes, the USPS makes roughly $8 million a year by selling this data.
Facebook: A Goldmine of Information
Everyone’s favorite social media site houses an incredible amount of information about them, and is arguably one of the best marketing tools available on the Internet. Other users can see what pages you have “Liked,” and can even suggest pages or friends to you. Due to this open-minded approach to social media, marketers are generally able to collect this data and use it to formulate the aforementioned lists. Even if you only host the minimal amount of personal data on your Facebook, there’s still a good chance that marketers can put you into a list judging from your liked pages and friends.
Whether we like it or not, companies and merchants are gathering our information and storing it for later use. Your business likely does something similar; collecting information about your own clients and storing it for later consumption.
By law, these institutions are allowed to collect this information, but there are others out there who seek out private information, like Social Security numbers, to commit identity fraud or steal your money. This begs the question of whether or not your business’s security solutions are up to snuff and able to protect your stored information from hackers.
When you deal with lots of personal information, like Social Security numbers or credit card numbers, you want to use the best security measures available. Total Tech Care can equip your business with a Unified Threat Management solution to keep your data safe from being compromised by hackers. This includes a firewall, spam blocking, and web filtering to keep the threats out, compounded by an antivirus to neutralize threats that get in. For more information about our UTM solution, give us a call at 866-348-2602.




